masonic cipher book pdf
Masonic cipher books, often found as PDF documents today, historically served to protect fraternal secrets and communications within Freemasonry.
These encoded texts represent a fascinating intersection of ritual, symbolism, and cryptographic practice, attracting both Masonic scholars and cryptography enthusiasts.
Historical Context of Masonic Ciphers
Masonic ciphers emerged in the 18th century, coinciding with the formalization of Freemasonry and a heightened emphasis on secrecy. Early lodges utilized simple substitution ciphers, evolving into more complex systems as the fraternity grew.
The need to safeguard rituals, passwords, and internal communications from outsiders fueled this cryptographic development. PDF versions of historical cipher manuscripts, like those detailing Daniel Parker’s Tablet, now offer researchers access to these intriguing documents.
These ciphers weren’t intended to be unbreakable by modern standards, but rather to deter casual observation and maintain a sense of mystery. The availability of digitized Masonic cipher books allows for broader study of their historical usage and evolution, revealing insights into the social and intellectual climate of the time.
The Need for Secrecy in Freemasonry
Secrecy has been a cornerstone of Freemasonry since its inception, stemming from the operative stonemasons’ need to protect their trade secrets. As the fraternity transitioned to a speculative society, this secrecy evolved to preserve ritualistic knowledge and a unique system of moral and philosophical teachings.
Masonic cipher books, increasingly available as PDF files, were instrumental in maintaining this confidentiality. They allowed members to communicate securely and record sensitive information without fear of unauthorized access.
The use of ciphers wasn’t about concealing nefarious activities, but rather about ensuring that Masonic teachings were only shared with those who had undergone proper initiation and demonstrated a commitment to the fraternity’s principles. Digitized resources now provide scholars with valuable insights into the methods used to uphold this tradition.
Daniel Parker’s Masonic Tablet
Daniel Parker’s Masonic Tablet, detailed in books available as a PDF, represents America’s earliest known cipher ritual, offering a unique glimpse into Masonic practices.
Overview of the Tablet’s Discovery
The Daniel Parker Masonic Tablet, a significant artifact in Masonic history, surfaced in the possession of the Parker family, descendants of the original owner. Its existence remained largely unknown to the broader Masonic world until its acquisition by the Scottish Rite, Northern Masonic Jurisdiction, in 1999.
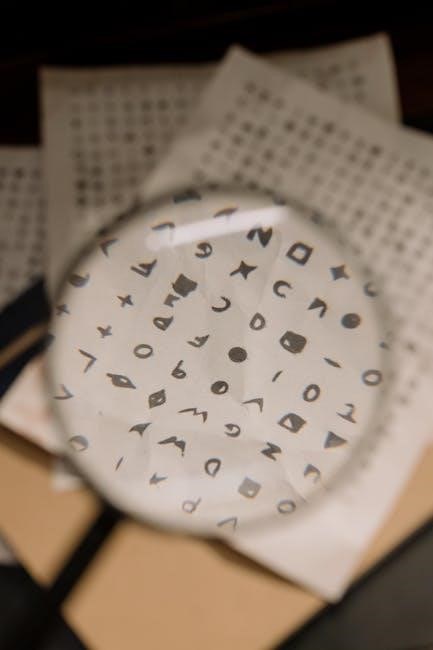
The tablet itself is a meticulously hand-drawn parchment, approximately 11 x 14 inches, covered in a complex array of symbols, geometric figures, and coded text. Initial assessments recognized its potential importance, prompting further investigation. The availability of information regarding the tablet, including detailed analyses, has increased with publications like Arturo De Hoyos’s work, often accessible as a PDF resource for researchers and enthusiasts.
Its discovery sparked considerable interest due to its unique cipher system and its potential to shed light on early American Masonic rituals and practices. The tablet’s condition and the fragility of the parchment necessitated careful preservation and study.
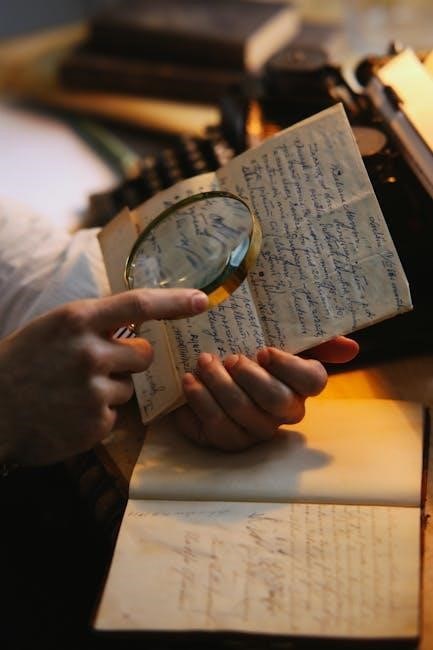
Arturo De Hoyos’s Decryption Work
Arturo De Hoyos, a renowned Masonic scholar and the Grand Archivist of the Scottish Rite, Northern Masonic Jurisdiction, spearheaded the extensive decryption efforts of the Daniel Parker Tablet. His meticulous research, detailed in his book “Daniel Parker’s Masonic Tablet,” unveiled the tablet’s secrets, revealing it as a ritual of initiation.
De Hoyos’s work involved identifying the cipher’s underlying principles, recognizing it as a complex combination of substitution and symbolic ciphers. He painstakingly correlated the symbols with known Masonic teachings and historical practices. His findings, often available in PDF format through Masonic libraries and online resources, demonstrate the tablet’s connection to York Rite Masonry.
The decryption process wasn’t immediate; it required years of dedicated study and collaboration with other experts. De Hoyos’s contribution is considered pivotal in understanding this unique piece of Masonic history.
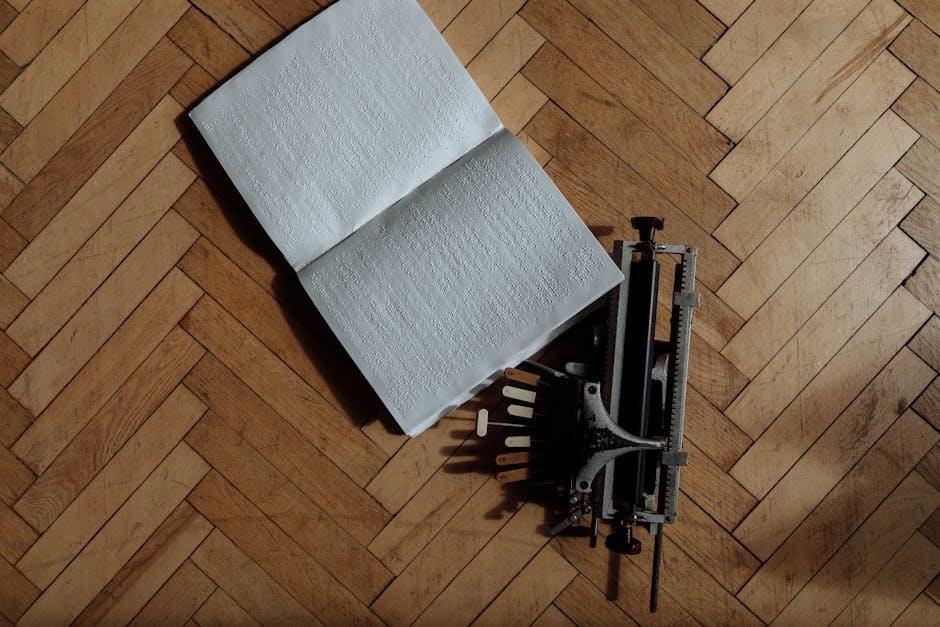
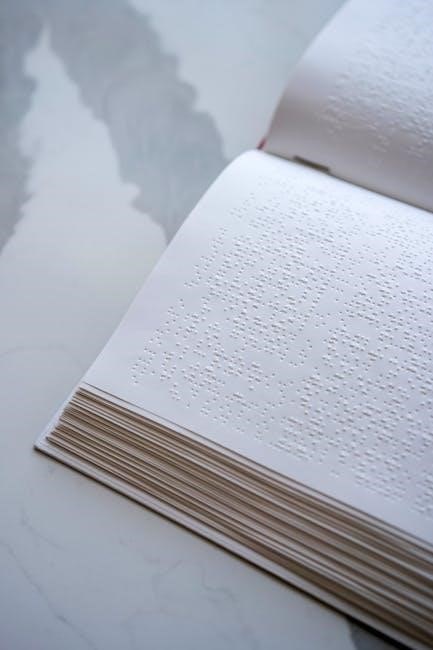
Facsimile and Reproduction of the Tablet
High-quality facsimiles and reproductions of the Daniel Parker Tablet are crucial for study, as the original is a delicate artifact. Arturo De Hoyos’s book, “Daniel Parker’s Masonic Tablet,” includes a detailed, full-color reproduction, allowing researchers to examine the cipher firsthand.
These reproductions, often available as digital images or in PDF format, preserve the tablet’s intricate details, including the hand-drawn symbols and layout. Access to these visual resources is vital for those attempting to understand the cipher or compare it to other Masonic documents.
Several Masonic libraries and historical societies offer access to these reproductions, ensuring the tablet’s information remains accessible to scholars and enthusiasts worldwide, fostering continued research and analysis.
Types of Masonic Ciphers
Masonic ciphers, often documented in PDF form, range from simple alphabetical substitutions to complex numerical and geometric systems, safeguarding fraternal knowledge.
Alphabetical Substitution Ciphers
Alphabetical substitution ciphers represent a foundational element within Masonic cipher book traditions, frequently encountered in digitized PDF versions of historical documents. These methods involve replacing each letter of the alphabet with another, creating a coded message.
Simple variations utilize a straightforward shift – for example, Caesar’s cipher – while more elaborate systems employ randomized alphabets or keyword-based substitutions. The key to decryption lies in discovering the substitution pattern, often hinted at within the cipher itself or through contextual clues related to Masonic ritual and symbolism.
Many early Masonic ciphers relied on these relatively straightforward techniques, making them accessible for initiates to learn and utilize, yet still providing a degree of secrecy against outsiders. The prevalence of these ciphers in surviving PDF copies underscores their historical importance.
Numerical Ciphers and Their Application
Numerical ciphers represent a significant category within Masonic cipher book systems, readily available for study in PDF formats of digitized historical texts. These ciphers assign numerical values to letters, often based on their position in the alphabet (A=1, B=2, etc.), or utilizing more complex gematria-like systems.
Masonic application frequently involved converting names, phrases, or ritual elements into numerical sequences, then manipulating these numbers through addition, subtraction, or other mathematical operations to create the ciphertext. Decryption requires reversing this process, often aided by knowledge of Masonic symbolism and numerological significance.
The use of numerical ciphers added a layer of complexity, appealing to the Masonic emphasis on mathematical principles and the pursuit of hidden knowledge, as evidenced in numerous PDF examples.
Geometric Ciphers in Masonic Symbolism
Geometric ciphers, often visually represented within Masonic cipher book illustrations – now accessible as PDF documents – intertwine cryptographic methods with core Masonic symbolism. These ciphers utilize shapes, lines, and spatial arrangements to conceal messages, drawing heavily on the significance of tools like the square, compass, and level.
Rather than simple letter substitution, geometric ciphers might encode information through the angles of a triangle, the number of points on a star, or the arrangement of symbols within a specific geometric pattern. Understanding the symbolic meaning of these shapes is crucial for decryption.
Analysis of these ciphers, often found in digitized PDF archives, reveals a sophisticated system where form and meaning are inextricably linked, reflecting Masonic beliefs about the universe’s underlying geometric order.
Decoding Masonic Cipher Books
Decoding these historical texts, often available as PDFs, requires a blend of cryptographic techniques and Masonic knowledge to unlock their concealed fraternal secrets.
Common Techniques for Cipher Breaking
Frequency analysis remains a cornerstone, examining the occurrence of symbols within a Masonic cipher book PDF to correlate them with common letters like ‘E’ or ‘T’.
Substitution pattern recognition is crucial, as many ciphers rely on replacing letters with symbols or numbers; identifying these patterns is key;
Keyword searching, leveraging known Masonic terms or names, can provide initial breakthroughs, especially when dealing with complex ciphers.
Contextual analysis, understanding the historical period and Masonic practices, aids in interpreting ambiguous symbols or phrases found within the PDF.
Furthermore, recognizing common cipher types – alphabetical, numerical, or geometric – narrows the decryption possibilities, accelerating the process of revealing hidden messages.
Tools and Resources for Decryption
For analyzing a Masonic cipher book PDF, online frequency analysis tools are invaluable, quickly revealing symbol distributions. Dedicated cryptography software, like CyberChef, offers diverse decryption algorithms and pattern recognition capabilities.
Historical Masonic resources, including digitized journals and ritual books, provide contextual clues and potential keywords. Websites specializing in cryptography, such as those offering cipher challenges, hone decryption skills.
Arturo De Hoyos’s work on the Daniel Parker Tablet, often available in book form or discussed online, offers insights into specific cipher techniques.

Furthermore, forums and communities dedicated to cryptography and Freemasonry facilitate collaborative decryption efforts, sharing knowledge and strategies for tackling complex PDF-based ciphers.
Challenges in Deciphering Historical Ciphers
Deciphering a Masonic cipher book PDF presents unique hurdles; many ciphers were deliberately obscure, relying on shared Masonic knowledge unavailable to outsiders. The age of the PDF and its source material introduces potential transcription errors or damaged text, complicating analysis.
Variations in cipher usage across different Masonic lodges and time periods mean a single decryption key may not universally apply. Limited context—understanding the intended message’s subject matter—hinders educated guesses.
Furthermore, some ciphers blend multiple techniques, requiring layered decryption. The intentional use of nulls, homophones, and deliberately misleading symbols adds complexity, demanding patience and a multi-faceted approach to unlock the secrets within the historical PDF.
Availability of Masonic Cipher Book PDFs
Masonic cipher book PDFs are increasingly accessible online, though legitimate sources are crucial for accurate transcriptions and avoiding copyright infringements.
Legitimate Sources for Digital Copies
Finding reliable digital copies of Masonic cipher books, often in PDF format, requires careful consideration of source legitimacy. Arturo De Hoyos’s work, specifically “Daniel Parker’s Masonic Tablet: A History, Decryption, and Facsimile of America’s First Cipher Ritual,” available on platforms like Amazon, provides a scholarly and legally obtained resource.
Academic institutions and Masonic libraries frequently offer digitized collections, ensuring authenticity and preservation. Reputable Masonic research societies may also provide access to their archives, including cipher manuscripts, through controlled digital access.
Furthermore, some Grand Lodges maintain online resources with historical documents, potentially including cipher materials. Always prioritize sources with clear provenance and copyright information to support ethical research and avoid legal issues when accessing Masonic cipher book PDFs.
Risks Associated with Downloading from Unverified Sources
Downloading Masonic cipher book PDFs from unverified sources presents significant risks. These files may contain malware, viruses, or other malicious software that can compromise your device and personal information. Illegitimate sources often distribute altered or incomplete versions of texts, hindering accurate research and potentially misrepresenting Masonic teachings.
Furthermore, obtaining materials from unauthorized platforms infringes upon copyright laws and supports illegal distribution. Such downloads may expose you to legal repercussions and contribute to the erosion of intellectual property rights.
The authenticity of content from untrusted websites is questionable, potentially leading to the study of fabricated or inaccurate cipher manuscripts. Prioritize legitimate sources to ensure data security and scholarly integrity when seeking Masonic cipher book PDFs.
Copyright Considerations and Fair Use
Masonic cipher book PDFs, like any published work, are subject to copyright laws. Reproducing, distributing, or altering copyrighted material without permission is illegal. However, “fair use” doctrines allow limited use of copyrighted material for purposes like scholarship, research, criticism, or education.
Determining fair use depends on factors like the purpose and character of the use, the nature of the copyrighted work, the amount used, and the effect on the market. Simply downloading a PDF for personal study may be permissible, but widespread distribution is not.
Researchers and scholars should carefully evaluate copyright restrictions and seek permission when necessary. Respecting intellectual property rights ensures the continued availability of these historical documents for legitimate study and preservation.
The Significance of Masonic Ciphers Today
Masonic cipher book PDFs offer modern researchers access to historical cryptographic practices, fueling academic study and preserving Masonic traditions for future generations.
Continuing Relevance in Masonic Ritual
Masonic cipher book PDFs, while primarily historical documents now, demonstrate a continuing thread of coded communication within Freemasonry. Though not typically used in the same way as in the 18th and 19th centuries, the principles of secrecy and symbolic representation inherent in these ciphers remain central to Masonic ritual work.
The study of these historical ciphers deepens a Mason’s understanding of the fraternity’s commitment to safeguarding its traditions and teachings. Modern Masonic education often incorporates discussions of these past methods, emphasizing the importance of discretion and the layered meanings embedded within Masonic symbolism.
Access to digitized versions, like those available as PDFs, allows lodges and individual Masons to explore these historical practices, fostering a greater appreciation for the ingenuity and dedication of their predecessors. The spirit of coded knowledge continues to resonate within the Craft.
Academic Study of Masonic Cryptography
The availability of Masonic cipher book PDFs has significantly fueled academic interest in Masonic cryptography. Researchers now have easier access to primary source material, enabling detailed analysis of cipher systems and their historical context. This has led to publications like Arturo De Hoyos’ work on Daniel Parker’s Tablet, offering comprehensive decryption and historical insights.
Scholars explore these ciphers not only as cryptographic curiosities but also as windows into the social and intellectual world of 18th and 19th-century Freemasonry. The study reveals connections between Masonic practices and broader trends in secret societies, Enlightenment thought, and the development of cryptography itself.
Digitized collections facilitate comparative analysis of different ciphers, identifying patterns and influences. These PDF resources are invaluable for understanding the evolution of Masonic symbolism and the methods used to protect its esoteric knowledge.
Influence on Modern Cryptography
While not directly foundational, the historical use of ciphers within Masonic cipher book PDFs offers intriguing parallels to the development of modern cryptography. The principles of substitution, transposition, and codebooks employed by Masons demonstrate an early understanding of cryptographic concepts.
Although these methods are relatively simple by today’s standards, they represent a practical application of secrecy and information security predating formalized cryptographic research; Studying these historical ciphers provides context for understanding the evolution of more complex systems.
The emphasis on symbolism and layered meaning within Masonic ciphers also hints at the importance of obfuscation and psychological factors in cryptography. Access to digitized PDF versions allows researchers to trace these early influences and appreciate the historical roots of information protection.


Leave a Reply
You must be logged in to post a comment.